1 概述 Overview
玄武上位机软件用来将电子控制器中的应用程序和数据,从PC端下载到电子控制器上。支持UDSonCAN、UDSonEth、UDSonK-Line、UDSonLIN协议。提供客户协议定制集成,广泛应用在电子控制器产品开发阶段,测试阶段,售后服务阶段。
ZC.XuanWu upper computer software is used to download application programs and data from the PC to the electronic controller. It supports UDS on CAN, UDS on Eth, UDS on K-Line, and UDS on LIN protocols. It offers customized integration of customer-specific protocols and is widely used in the development, testing, and after-sales service stages of electronic controller products.
知从玄武程序刷新与诊断测试工具可应用于OEM和Tier1多种应用场景下。用户可以方便的在实验室,试验车辆以及实车上方便的进行程序刷写工作。
ZC.XuanWu program refresh and diagnostic testing tools can be applied in various application scenarios for OEMs and Tier 1 suppliers. Users can conveniently perform program flashing work in laboratories, test vehicles, and actual vehicles.
玄武上位机软件目前应用于各类电子控制器的程序刷写:
ZC.XuanWu upper computer software is currently used for program flashing of various electronic controllers:
Ø 车身控制器Body Control Module (BCM)
Ø 空调控制器Air Conditioning Controller
Ø DC/DC控制器DC/DC Converter
Ø 电子助力转向控制器Electric Power Steering Controller
Ø 发动机控制器Engine Management System (EMS)
Ø 变速箱控制器Transmission Control Module (TCM)
Ø 电池管理系统Battery Management System (BMS)
Ø 整车控制器Vehicle Control Unit (VCU)
Ø 电机控制器Motor Control Unit (MCU)
Ø 电动助力转向系统Electric Power Steering System (EPS)
Ø 防抱死制动系统Anti-lock Braking System (ABS)
Ø 电子稳定性控制程序Electronic Stability Program (ESP)
Ø 主动防撞系统Active Collision Avoidance System (ACC)
Ø 牵引力控制系统Traction Control System (TCS)
Ø ADAS控制器Advanced Driver Assistance Systems Controller
配置环境Configuration Environment | |
Hardware | PCAN、Mongoose、Kvaser、USBCAN(ZLG)、VN1640、TC1016、OBD-RJ45 |
Configuration Environment | Win7/10 64bit |
玄武上位机支持下述设备:

2 VBF文件介绍 VBF File Introduction
在智能网联汽车“软件定义车辆”的时代背景下,整车电子电气架构日趋集中化,ECU(电子控制单元)软件迭代频率从年级缩短至周级甚至天级。海量的固件升级任务通过 OTA(空中下载技术)下发至车辆,这对刷写过程的安全性、完整性及工程效率提出了前所未有的挑战。在此背景下,VBF(Versatile Binary Format,通用二进制格式)文件 成为确保安全、可靠、可管控的 ECU 刷写的关键数据载体。此外,在汽车信息安全与功能安全领域,VBF 文件与数字签名、加密技术形成了协同防护体系。通常采用 “先签名后加密” 或 “先计算哈希后传输” 的处理流程——即对原始固件生成数字签名并嵌入 VBF 结构,再对整体文件进行可选的加密传输。这种方式不仅能通过签名机制防止非法固件刷入,还能借助 VBF 内嵌的多级校验块(如 RootHash、CRC)在刷写前、传输中、写入后分别验证数据完整性,使中间人攻击、固件篡改和回滚攻击难以得逞。
Against the backdrop of the "software-defined vehicle" era in connected and autonomous electric vehicles, the overall vehicle E/E architecture is becoming increasingly centralized. The iteration frequency of ECU software has shortened from yearly to weekly or even daily cycles. Massive firmware upgrade tasks are delivered to vehicles via OTA (Over‑The‑Air) technology, posing unprecedented challenges to the security, integrity, and engineering efficiency of the flash programming process. In this context, the VBF (Versatile Binary Format) file has become a key data carrier for ensuring safe, reliable, and controllable ECU flashing. Furthermore, in the fields of automotive cybersecurity and functional safety, the VBF file forms a collaborative protection system together with digital signatures and encryption technologies. The typical processing flow follows a "sign‑then‑encrypt" or "hash‑then‑transmit" approach – i.e., generating a digital signature on the original firmware, embedding it into the VBF structure, and then optionally encrypting the entire file for transmission. This method not only prevents illegal firmware from being flashed through the signature mechanism, but also leverages the multi‑level verification blocks embedded in VBF (such as RootHash and CRC) to validate data integrity before flashing, during transmission, and after writing. As a result, man‑in‑the‑middle attacks, firmware tampering, and rollback attacks are rendered much more difficult.
VBF文件主要由三大部分组成:文件头(Header)、数据块(Data Blocks) 和 校验块(Verification Block)。文件头以ASCII文本形式存储目标ECU地址、擦除参数、版本号等刷写元数据;数据块承载实际的固件代码或校准数据,可分段存储并支持压缩算法;校验块则包含RootHash、双重数字签名及CRC校验值,用于在刷写前、传输中和写入后验证文件的完整性与真实性。
A VBF file mainly consists of three parts: Header, Data Blocks, and Verification Block. The Header stores flash programming metadata such as target ECU address, erase parameters, and version number in ASCII text format. The Data Blocks carry the actual firmware code or calibration data, which can be stored in segments and support compression algorithms. The Verification Block contains the RootHash, dual digital signatures, and CRC check values, used to verify the integrity and authenticity of the file before, during, and after the flash programming process.
2.1 VBF文件详细介绍 Detailed Introduction to the VBF File Structure
VBF(Versatile Binary Format,通用二进制格式)作为一种结构化混合格式文件,与HEX、S19等传统固件格式不同,VBF在单纯存放二进制数据的基础上,增加了丰富的元数据描述和多层级安全校验机制,是一个集配置指令、二进制固件、完整性校验和数字签名于一体的混合封装格式。
VBF (Versatile Binary Format) is a structured hybrid format file. Unlike traditional firmware formats such as HEX and S19, which simply store binary data, VBF adds rich metadata descriptions and multi‑level security verification mechanisms. It is a hybrid packaging format that integrates configuration instructions, binary firmware, integrity checks, and digital signatures.
从整体结构来看,VBF文件由三大核心部分组成:版本段、文件头段和数据段。在VBF 2.6及以上版本中,数据段内部还嵌套了VBT(校验块表) ,文件末尾还独立存在Verification Block(校验隔离区) ,后者存放着整包的安全总成——RootHash和双重数字签名。以下对每个部分进行详细介绍。
From an overall structural perspective, the VBF file consists of three core parts: the version segment, the header segment, and the data segment. In VBF version 2.6 and above, the data segment internally embeds a VBT (Verification Block Table), and at the end of the file there exists an independent Verification Block, which stores the entire package’s security assembly — the RootHash and the dual digital signatures. Each part is described in detail below.
文件头段(Header):
文件头段(Header)紧接在版本段之后,以ASCII文本形式存储,并用大括号包裹整个字段集合,是VBF文件中定义刷写流程元数据与配置指令的核心区域。该段包含了软件零件号(sw_part_number)、软件版本(sw_version)、软件包类型(sw_part_type)、ECU物理目标地址(ecu_address)、擦除区间列表(erase)、程序入口地址(call)、校验块表起始地址与长度(verification_block_start / length)、RootHash值(verification_block_root_hash)以及文件级CRC32校验和(file_checksum)等关键字段。Header段的作用是为解析工具和ECU提供刷写前必须的兼容性检查、地址映射、Flash擦除规划及安全校验定位信息,直接决定了固件能否被正确识别、加载并安全写入目标ECU。
The Header segment immediately follows the version segment. It is stored in ASCII text format, with the entire field set enclosed in curly braces. It serves as the core area within the VBF file that defines the flash programming metadata and configuration instructions. This segment contains key fields such as the software part number (sw_part_number), software version (sw_version), software part type (sw_part_type), ECU physical target address (ecu_address), erase area list (erase), program entry address (call), verification block table start address and length (verification_block_start / length), RootHash value (verification_block_root_hash), and file‑level CRC32 checksum (file_checksum). The role of the Header segment is to provide the parsing tool and the ECU with the necessary pre‑flash compatibility checks, address mapping, Flash erase planning, and security verification locating information. It directly determines whether the firmware can be correctly identified, loaded, and safely written to the target ECU.
数据段(Data Blocks):
数据段以纯二进制格式存储,是整个VBF文件中实际承载固件代码或标定数据的核心载体。该段由多个连续排列的数据块(Block)构成,每个Block均包含4字节起始地址、4字节数据长度、n字节有效二进制数据以及2字节CRC-16校验位。数据段的作用是为解析工具和ECU提供分段可寻址、可校验的刷写数据映像,支持将不同功能的代码或数据分散存放于Flash的不同地址区间,并在刷写过程中通过块级CRC校验保证每段数据传输的完整性
The Data Segment is stored in pure binary format and serves as the core carrier within the entire VBF file that actually holds the firmware code or calibration data. This segment consists of multiple consecutively arranged data blocks. Each block contains a 4‑byte start address, a 4‑byte data length, n bytes of valid binary data, and a 2‑byte CRC‑16 checksum. The role of the Data Segment is to provide the parsing tool and the ECU with a segmented, addressable, and verifiable flash programming data image. It supports the分散存放 (distribution) of code or data with different functions across different address ranges of the Flash memory, and ensures the integrity of each data block during the flash programming process through block‑level CRC verification.
校验块表(Verification Block Table):
VBT段并非独立于数据段的区域,而是数据段中一个具有特殊身份的数据块。该块内部存放的是数据段内除自身以外所有其他Block的哈希值列表(每个哈希值采用SHA-256算法计算),同时记录了各Block的起始地址与长度信息。VBT的核心作用是为数据段的整体完整性建立“集体指纹”——解析工具或ECU读取VBT后,对其整体(起始地址、长度、哈希表数据)再次进行SHA-256运算,得到RootHash,进而与文件头段中的verification_block_root_hash字段进行比对。通过这一设计,VBT将分散在各个数据块中的内容通过哈希链汇聚成一个可被数字签名保护的安全锚点,实现了从“单个Block校验”到“全数据段防篡改”的信任传递。
The VBT segment is not an area independent of the Data Segment; rather, it is a data block with a special identity within the Data Segment. Inside this block is stored a list of hash values (each hash calculated using the SHA‑256 algorithm) of all other blocks within the Data Segment except itself, along with the start address and length information of each block. The core function of the VBT is to establish a "collective fingerprint" for the overall integrity of the Data Segment – after the parsing tool or ECU reads the VBT, it performs a SHA‑256 operation on the entire VBT content (start address, length, hash table data) to obtain the RootHash, which is then compared with the verification_block_root_hash field in the Header segment. Through this design, the VBT aggregates the content distributed across individual data blocks via a hash chain into a single security anchor that can be protected by digital signatures, achieving a trust transfer from "single‑block verification" to "full Data Segment tamper‑proofing".
签名段(Verification Block):
签名段(Verification Block,校验块)位于VBF文件的末尾(VBF 2.6及以上规范),以二进制格式独立存放,是整个文件的安全总成与信任锚点。该段承载了两类核心安全数据:RootHash值与双重RSA-2048数字签名(研发签名 sw_signature_dev 和生产签名 sw_signature)。其作用是为ECU提供固件来源可信性与完整性的终极验证依据——ECU在执行刷写前,首先从签名段提取数字签名并使用内置公钥解密,得到理论上应匹配的RootHash;同时,从数据段中定位VBT,对其执行SHA-256哈希运算得出实际RootHash;将两者进行比对,若一致则证明固件自生成后未被篡改且来自合法持有私钥的签发方(Tier1或OEM)。通过将签名段置于文件末尾并与文件头段中的 verification_block_root_hash、verification_block_start/length 等字段形成交叉引用,VBF实现了从固件内容 → VBT → RootHash → 数字签名的全链路防篡改信任传递。
The Signature Segment (Verification Block) is located at the end of the VBF file (VBF version 2.6 and above), stored independently in binary format. It serves as the security assembly and trust anchor for the entire file. This segment carries two core types of security data: the RootHash value and dual RSA‑2048 digital signatures (the development signature sw_signature_dev and the production signature sw_signature). Its role is to provide the ECU with the ultimate verification basis for firmware source authenticity and integrity – before performing a flash programming operation, the ECU first extracts the digital signature from the Signature Segment and decrypts it using the built‑in public key, obtaining the theoretically expected RootHash. Simultaneously, it locates the VBT within the Data Segment and performs a SHA‑256 hash operation on it to derive the actual RootHash. The two are then compared; if they match, it proves that the firmware has not been tampered with since its generation and originates from a legitimate signer (Tier‑1 or OEM) holding the corresponding private key. By placing the Signature Segment at the end of the file and creating cross‑references with fields such as verification_block_root_hash, verification_block_start/length, etc., in the Header segment, VBF achieves a full‑chain tamper‑proof trust transfer from: firmware content → VBT → RootHash → digital signature.
3 玄武VBF文件下载功能介绍 Introduction to Xuanwu VBF File Download Function
3.1 VBF文件传输配置 VBF File Transfer Configuration
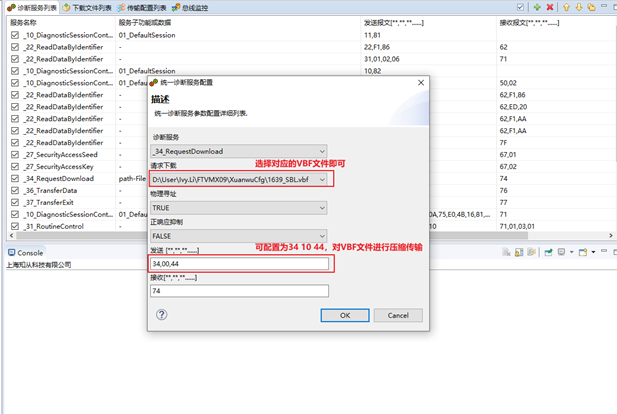
玄武支持用户向ECU发送单条或多条诊断报文,针对VBF文件刷写,玄武支持在新建UDS 0x34服务时进行配置,选择_34_RequestDownload,点击Path-File选择文件,并可配置为34 10 44,选择压缩传输或正常刷写
Xuanwu supports users in sending single or multiple diagnostic messages to the ECU. For VBF file flashing, Xuanwu allows configuration when creating a new UDS 0x34 service: select _34_RequestDownload, click Path‑File to choose the file, and configure it as 34 10 44, then select either compressed transmission or normal flashing.
玄武默认 dataFormatIdentifier为0x00,用户需要配置刷写文件起始地址、刷写文件Size。
Xuanwu defaults the dataFormatIdentifier to 0x00. The user needs to configure the start address of the flash file and the size of the flash file.
3.2 VBF文件签名传输配置 VBF File Signature Transfer Configuration
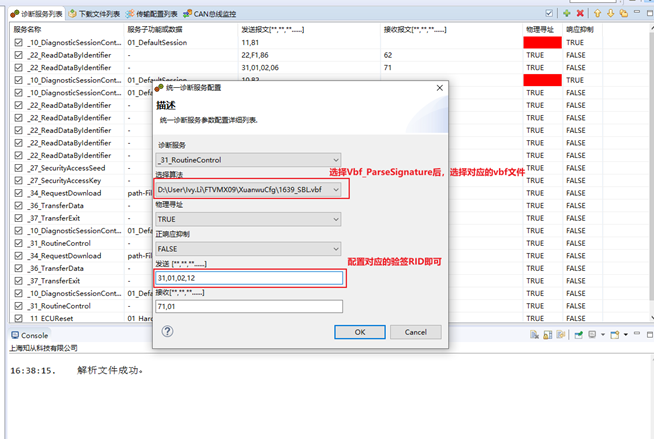
玄武支持用户向ECU发送VBF文件中的Signature,支持在新建UDS 0x31服务时进行配置,选择_31_RoutineControl,点击VBF-Signature选择文件,并配置31服务对应的RID即可,玄武会自动读取VBF文件中对应的签名,从而进行刷写过程中的验签操作。
Xuanwu supports users in sending the signature from a VBF file to the ECU. It allows configuration when creating a new UDS 0x31 service: select _31_RoutineControl, click VBF‑Signature to choose the file, and configure the RID corresponding to the 0x31 service. Xuanwu will then automatically read the corresponding signature from the VBF file to perform signature verification during the flashing process.
4 证书CERTIFICATE

玄武软件著作权登记证书
XUANWU SOFTWARE COPYRIGHT REGISTRATION CERTIFICATE